How-To
Protecting Your Hikvision CCTV DVR NVR from Vulnerabilities: Step-by-Step Guide to Secure Your Surveillance System
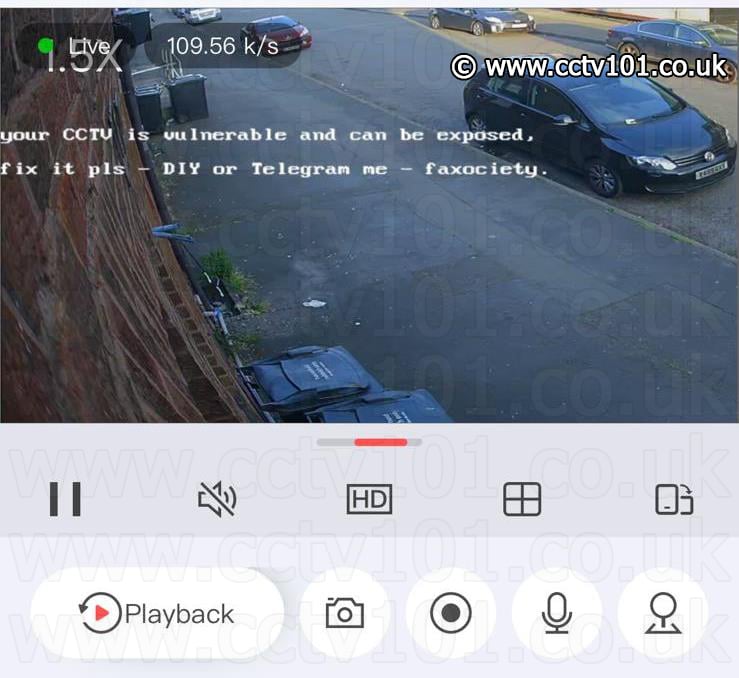
In this article we discuss the Hikvision vulnerability that allows anyone on the internet to gain full control of your Hikvision CCTV cameras or recorder and alter the device settings. In this case, an ethical hacker by the name ‘faxociety’ alerts users of their vulnerable system by altering the camera OSD to:
“Your CCTV is vulnerable and can be exposed, fix it pls – DIY or Telegram me – faxociety“
Follow this guide to secure your Hikvision CCTV cameras or recorder.
How did it happen?
In 2021, a British security researcher, known as Watchful_IP, discovered a command injection vulnerability affecting a number of Hikvision’s CCTV cameras and recorders. The vulnerability required no user input and bypassed the device login and was classified as critical, posing the highest level of risk. The researcher reported the vulnerability to Hikvision and was subsequently assigned the identifier CVE-2021-36260 in the NVD and a firmware update was released for affected devices to address the vulnerability.
The vulnerability relies on an affected device to be reachable from the internet and is in part aided by poor network security and lack of maintenance for a bad actor to gain unauthorised access.
Step 1. Disable UPnP & check for unknown user accounts
Access the Hikvision device’s web interface and browse to the following menu Configuration -> Network -> Basic Settings -> NAT
Then disable Enable UPnP and hit Save.
Disable UPnP on your router too. Refer to your ISP or router manufacturers manual on how to do this.
Next browse to Configuration -> System -> User Management
You will normally see a single account with the User Name admin. If you find any additional users that you do not recognise, delete them to prevent unauthorised access.
Step 2. Update your device firmware
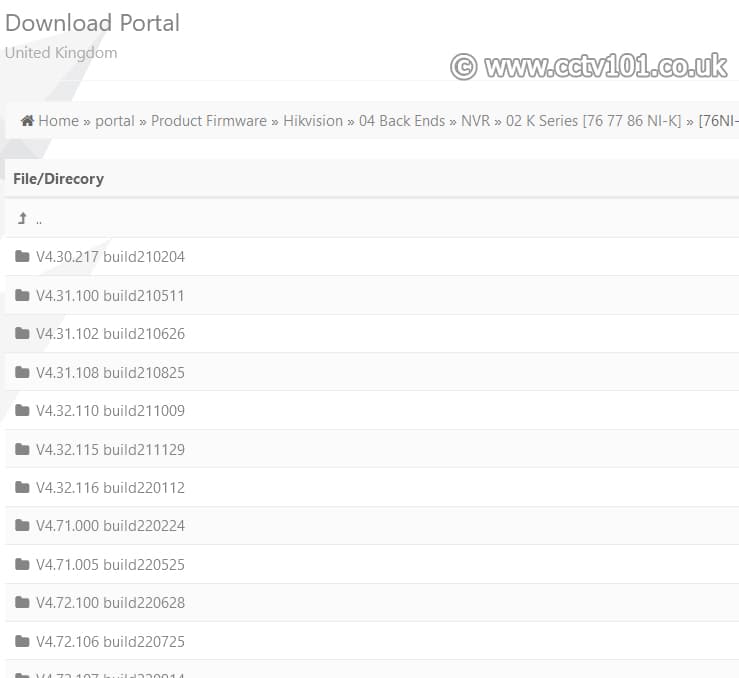
This vulnerability affects firmwares prior to build 210625. Locate the firmware for your specific Hikvision device on the Firmware Portal. It is good practice to regularly update your devices to stay protected against new threats. We recommend updating your Hikvision equipment at least once every 12 months or as instructed by an Hikvision Approved Installer.
In response to security threats, Hikvision have released a search tool for important security firmware updates. You can read more by clicking here.
If you have a third party router that wasn’t provided by your ISP, check that the router is updated and on the latest firmware.
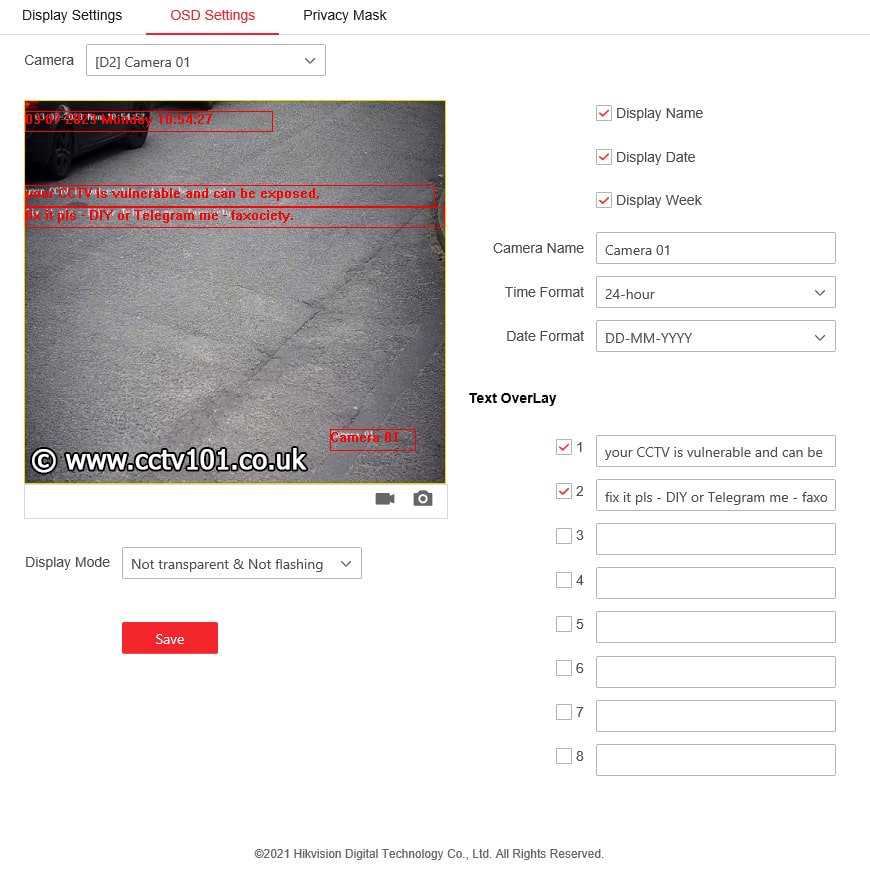
Step 3. Remove the OSD text overlay
Now that your device is secure and no longer accessible from the internet, it’s time to remove the text overlay. Access the Hikvision device’s web interface and browse to the following menu Configuration -> Image -> OSD Settings
Select the camera from the dropdown list and empty out the text in all of the the Text OverLay list and uncheck all boxes and hit Save. Repeat this process for all cameras affected.
Step 4. Secure your network & device passwords
If your CCTV camera or recorder is compromised, its time to look take a look at your network security. You should check your router firewall security settings and update your router to the latest firmware. Avoid using passwords that are common or easy for a brute force bot to crack. Set a unique password for all your online accounts and IoT devices and use a password manager to store and generate strong passwords for each device.
Network Security Tips
Port Forwarding
Hikvision recorders and cameras no longer require port forwarding for remote access. If you are still using port forwarding, we recommend to switching to the P2P method of connection as it is the easiest to use and manage users via a Hik-Connect app.
If you require ports open, it is advised to forward the Hikvision device’s internal server port (8000) to a random external port in the 1024 – 65535 range. If your router is capable of IP filtering or has a built-in VPN server, we recommend utilising these features.
Beef up your security with a firewall router
A business should not be using a standard ISP supplied router for its main routing, we suggest a hardware firewall router capable of packet level filtering and proactive rule based IP blocking.
Create a separate VLAN for your cameras
Create a VLAN and separate your CCTV traffic from your computer network. This will isolate your CCTV system and prevent users and their apps tinkering with your CCTV system.
Don’t give out your WiFi password
Never give out your main WiFi password to guests and visitors. If you must, set up a separate guest WiFi network to isolate temporary users from accessing devices on your main network.
Summary
It is important to take a proactive approach to any IoT devices connected to the internet from your home or business. All devices which connect to the internet are at risk of being hijacked or compromised.
Stay up to date with latest security threats and ensure you adhere to best network practices to keep your devices secure from hackers.
Hikvision are trade only products and it is recommended to contact a Hikvision Certified Installer who can provide you with a better experience.
You can contact us for help & support with your Hikvision products.